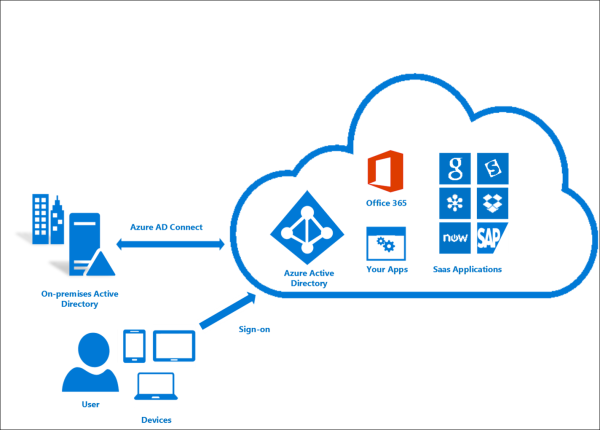
There are two frequent issues when it comes to cloud computing: security and control. Yes, of course. But it’s something we all need to understand. Is it possible to influence what lies beyond our borders? Is your network not protected by a firewall? When discussing future changes in on-premises and cloud installations, the question of user management and authentication will come up. You’ll be directed to identity providers as a result of this. There are a slew of them, including Microsoft, Ping, Centrify, and a slew of others.
Let’s look at one of them today: Azure Active Directory (or, in short, Azure AD, mostly searchable on the web). Does this ring a bell? We probably have something for that, and it is called Active Directory, and it’s been around for a long time. It’s also functioning! So, do we require another? Is this merely about sales? Let’s know more about the Azure Active Directory through this blog.
Quick Facts about A1 “34
We all refer to Active Directory as Active Directory Domain Services (or AD DS for short). It’s an on-premises directory that handles user and service authentication and authorization. You can control access to resources such as applications and file sharing for your on-premises users. Simple!
For authentication and SSO, AD DS uses the Kerberos protocol. Yes! SSO for applications is possible with AD DS. It only necessitates a suitable application configuration. It works with LDAP. It is a data access protocol, but it’s also used for user authentication in many programs.
Tip: If someone tells you that these pop-up windows requesting a domain username and password are by design, challenge them! They certainly aren’t! The majority of the time, it boils down to correcting Kerberos settings.
What AD DS can’t help you with: Authentication of users that aren’t on your network. You can, however, technically do it! It will necessitate some further efforts in software or hardware for publishing apps (reverse proxy, F5, Netscaler, did you remember anything?).
Few Questions that Explains More About Azure Active Directory
If you want a thorough understanding of Azure you can opt for an Azure online course.
Is Azure Active Directory similar to Active Directory?
No, it’s not. It employs technology that has its origins in AD. In a technical sense, Azure Active Directory is similar to on-premises Active Directory, but it does not work in the same way.
Is it Possible to replace my domain controllers?
No, it isn’t going to happen. Azure Active Directory is a cloud-based identity management service. It will not be able to take the place of your present AD. Its objective is to connect your current Active Directory to third-party apps and services.
Why should I consider it when this is not the same and cannot be replaced by my current AD?
You don’t have to bother if you stay on-premises. This is where it comes into play if you use externally provided software or SaaS programs like CRM, Google Apps, or Office 365. Do you wish to develop applications hosted outside your network (think AWS, Azure, or a hosting provider) or go mobile? You might want to look into this service once more.
Why can I not use any Local AD instead of Azure AD?
Azure Active Directory was built from the ground up with SaaS in mind. It supports protocols such as OpenID Connect, OAuth, or SAML to enable SSO and access control for those applications. Consider this scenario: your company wants to use an externally hosted CRM (such as SalesForce, Microsoft CRM, or Hootsuite), and you require easy access to it. Azure Active Directory is helpful in this situation.
Isn’t it possible for a local AD to grant access to those?
It can, but it will always require an external solution to operate as Azure AD. You have to deploy and manage it on your own.
What can’t Azure AD do for me (that local AD can right now)?
It’s possible to connect your PCs to Azure Active Directory, but it’s not the same as joining an AD domain. You can’t presently utilize Azure AD to secure file sharing, on-premises applications, or deploy GPOs to users using the conventional AD approach. Local groups or printers are currently unavailable in Azure Active Directory. We’re still waiting for the two environments to merge, but it’ll be available with Windows Server 2016.
Is it only for Microsoft applications, or can it be used for other applications too?
No. It adheres to common standards and protocols, allowing you to integrate it with third-party programs such as Google, Salesforce, and ServiceNow.
Do I need Azure Active Directory if we’re going to use Azure IaaS or AWS?
No, this isn’t a requirement in general. Azure AD is the underlying Azure security. Thus if you use Azure infrastructure (VMs, websites), you’ll get it. In that sense, you’ll use it to manage infrastructure access, but you’re not obligated to use it for anything else.
It does, however, add a security layer, so you should consider analyzing its features — it can also be used to grant access to Amazon AWS. You only need one solution to manage user access to both clouds in this situation.
Is it necessary for me to manage it independently from my present AD?
No! You can utilize tools to synchronize both environments and manage your AD.
Conclusion:
No, if you’re not using SaaS apps or not dealing with external or mobile consumers. In another scenario, Azure Active Directory or a comparable solution will be required sooner or later. Our experience has shown us that it’s best to check out current platforms before attempting to construct your solution in this area. It’s also good to start by defining your requirements and expectations and then developing your plan instead of jumping into the action first.